LinkedIn Has a Trust Problem. Decentralized Identity Can Fix It.
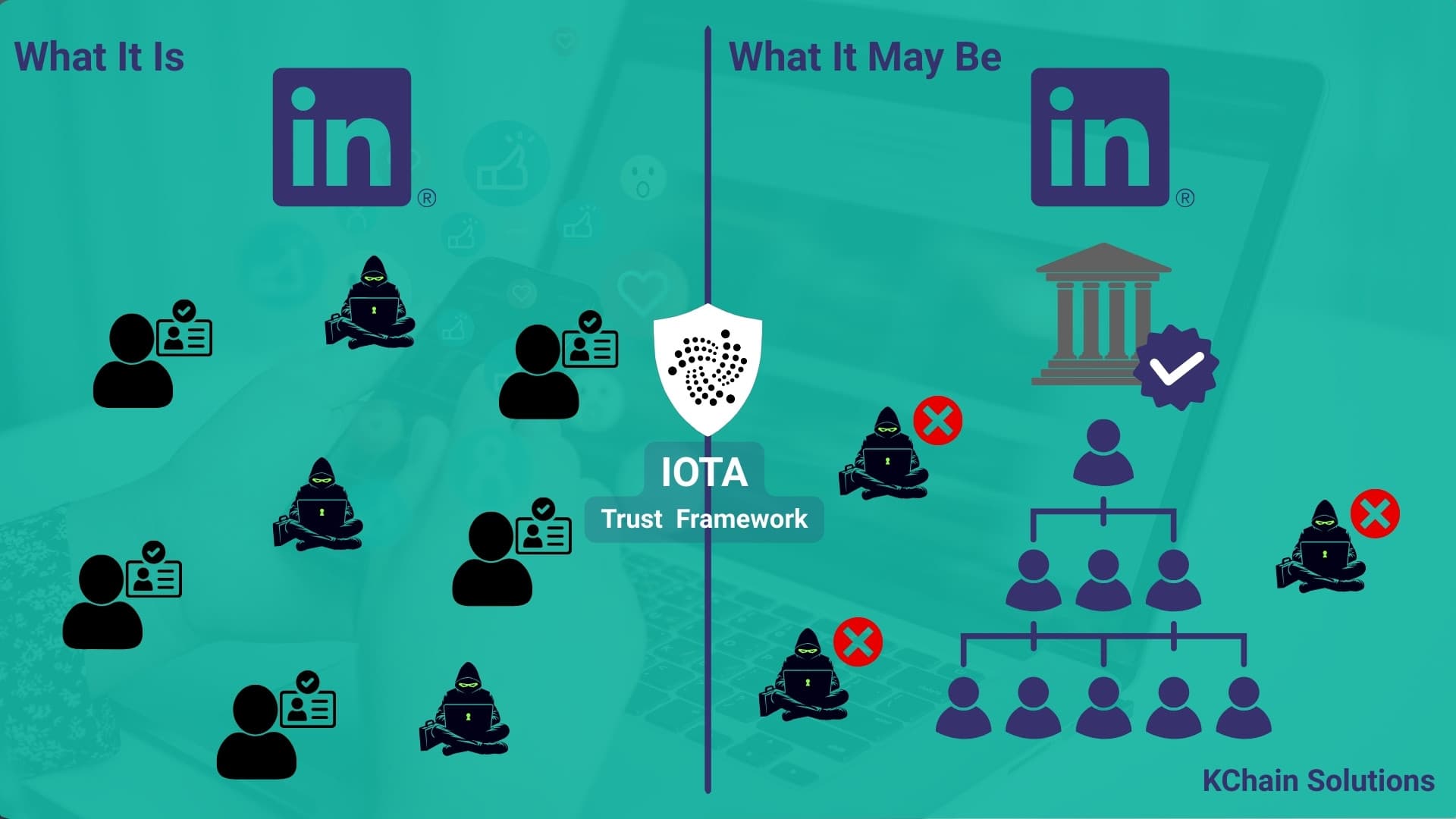
Who has never interacted with a fake or spam account on LinkedIn? Profiles trying to sell us marketing campaigns of dubious effectiveness, or proposing exotic job opportunities that turn out to be scams. We have all seen them. Most of us have learned to ignore the obvious ones.
But the obvious ones are disappearing. With AI, scammers can now generate professional headshots, write convincing work histories, build realistic company websites, and craft personalized messages that pass the "sounds like a real person" test. The fake accounts are becoming indistinguishable from real ones.
This is no longer just an annoyance. It is a systemic security problem, and LinkedIn's current defenses are not keeping up.
The Scale of the Problem
LinkedIn’s fake account problem has evolved from a nuisance into a significant security and trust issue.
Reports suggest that fake profiles and coordinated fraud campaigns are widespread, and research indicates that many organizations and individuals have encountered sophisticated false identities in remote hiring scenarios.
Threat actors increasingly use false professional identities not only to spread spam or scams, but to gain access to organizations. In some cases, individuals have secured remote roles under fabricated identities, creating direct exposure inside corporate environments.
LinkedIn itself removes tens of millions of inauthentic accounts each year, yet some still evade detection, creating potential risks when profiles are used to gain access to corporate systems or influence hiring outcomes.
Why LinkedIn's Current Approach Falls Short
LinkedIn's verification tools today rely on centralized, platform-controlled mechanisms:
- Email verification - Proves you have access to a corporate email. Does not prove you actually work there.
- ID verification - Proves you are a real person. Does not prove your professional claims are accurate.
- Company page badges - The company is verified, but there is no cryptographic link between the company and its listed employees.
The fundamental problem: LinkedIn is both the issuer and the verifier of professional identity. If the platform's detection fails, there is no independent way to validate that "Jane Doe, VP Engineering at Acme Corp" actually holds that position.
What is missing is a cryptographic link between an organization and its employees that anyone can verify independently, without relying on LinkedIn's systems.
The Solution: Decentralized Identity for Professional Verification
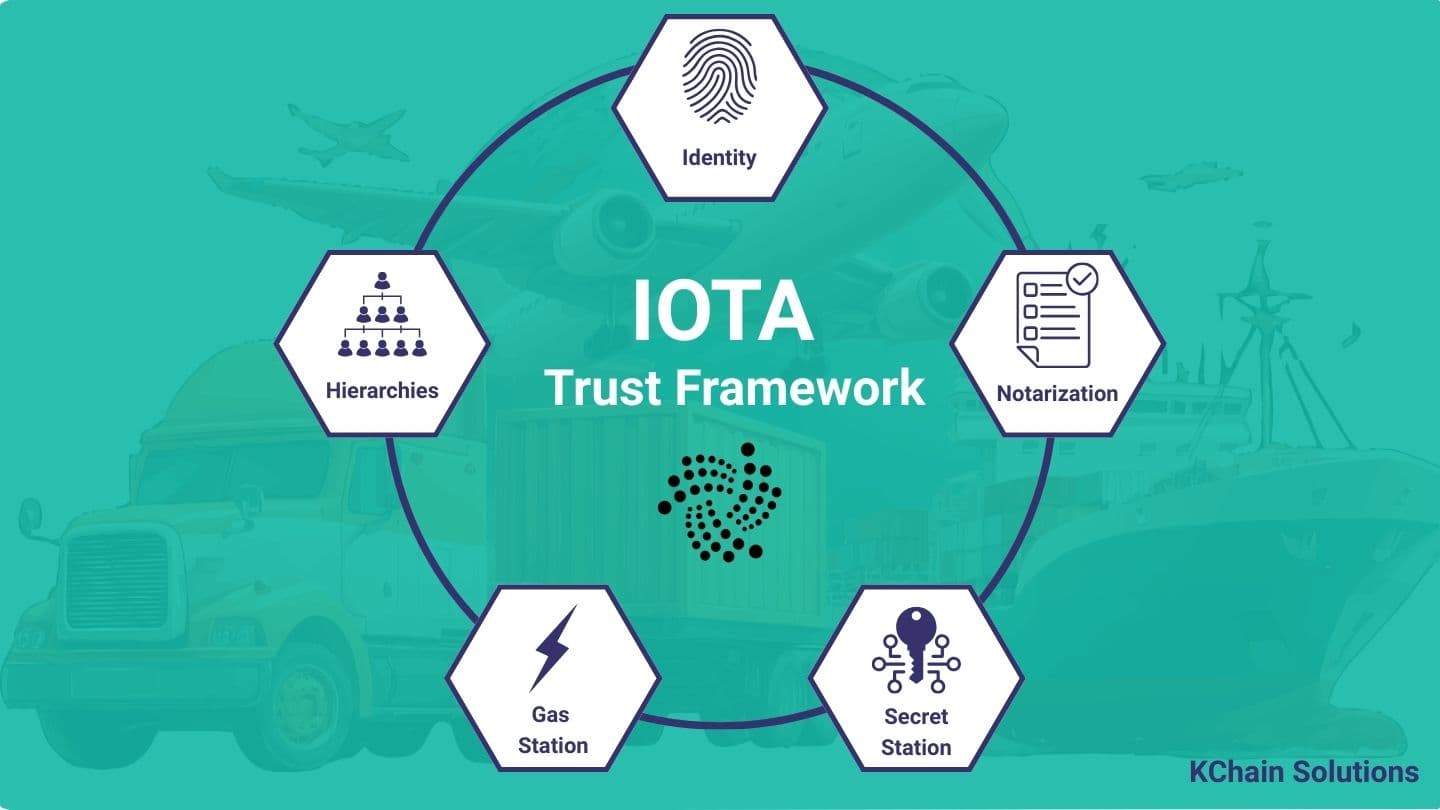
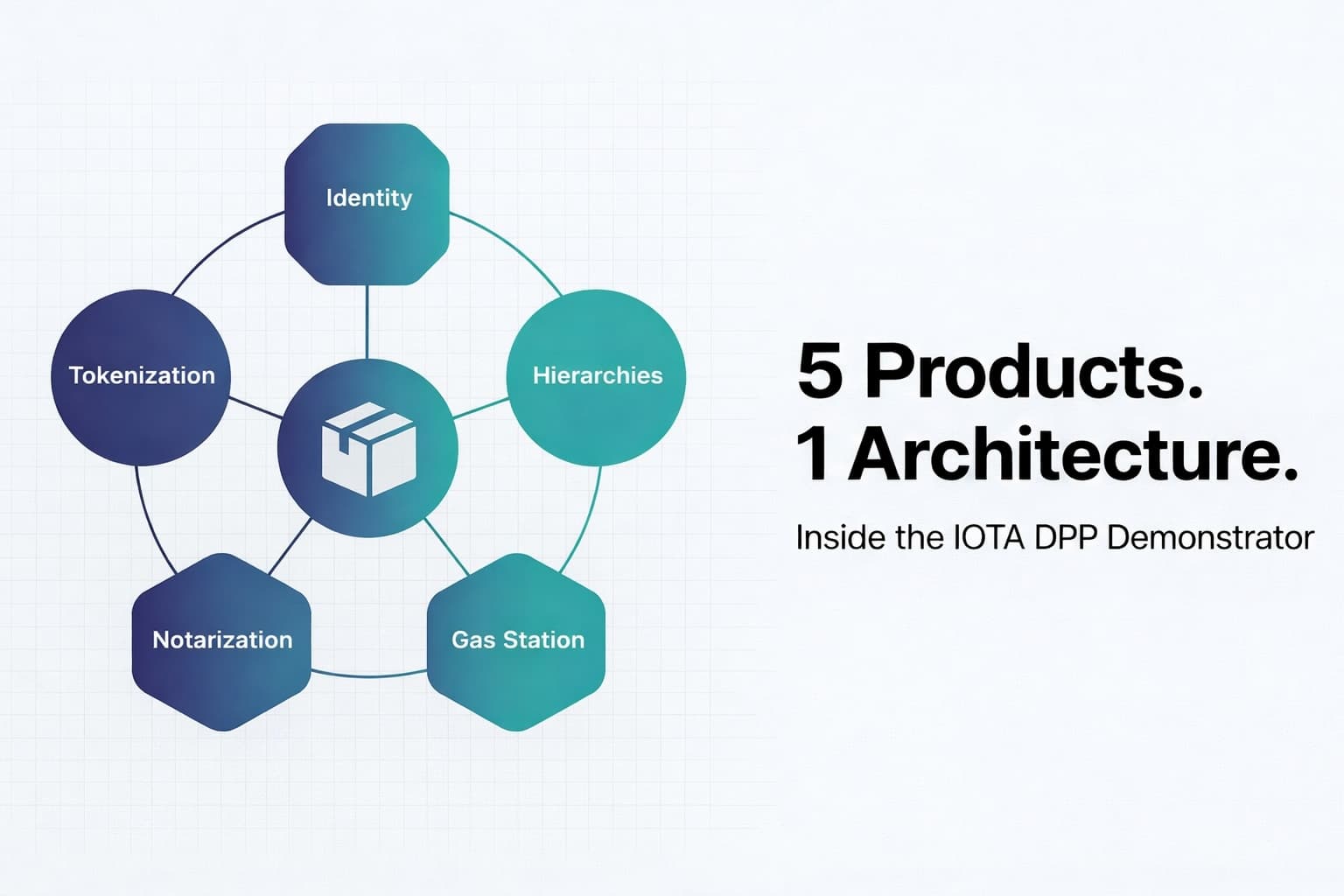
The IOTA Trust Framework provides the building blocks to solve this problem using two components: IOTA Identity (with Domain Linkage and Verifiable Credentials) and IOTA Hierarchies.
Here is how the pieces fit together.
Step 1: Enterprise Creates a Decentralized Identifier (DID)
An organization creates a DID anchored on the IOTA blockchain. This DID is a globally unique, cryptographically verifiable identifier that the organization controls.
But a DID alone does not prove anything about the real world. A scammer could create a DID and claim to be "Acme Corp." This is where Domain Linkage becomes critical.
Step 2: Domain Linkage Ties the DID to the Real World
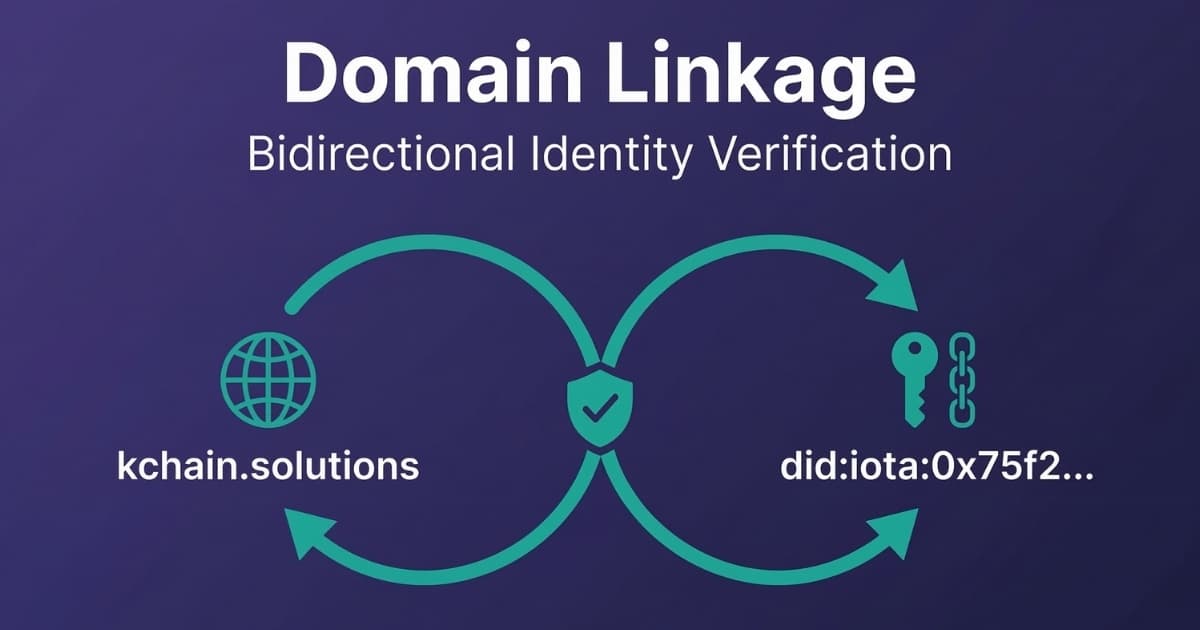
Domain Linkage is a W3C specification that creates a bidirectional cryptographic proof between a DID and a web domain.
The organization publishes a .well-known/did-configuration.json file on their website (e.g., https://acme.com/.well-known/did-configuration.json). This file contains a Domain Linkage Credential that proves: "The entity that controls acme.com is the same entity that controls this DID."
Anyone can verify this independently by:
- Resolving the DID on the IOTA blockchain
- Fetching the Domain Linkage Credential from the company's website
- Verifying the cryptographic signatures match
This is the key insight: if you trust acme.com (the real company website), you can now cryptographically verify their DID. No intermediary needed.
Step 3: LinkedIn Accredits Enterprises via Hierarchies
IOTA Hierarchies establishes a structured trust chain on-chain. In this model, LinkedIn itself is the root authority of the hierarchy. Companies that want to participate in verified professional identity must be accredited by LinkedIn as nodes in the hierarchy.
This creates a verifiable federation:
- LinkedIn (root authority of the IOTA Hierarchy)
- Accredits: Acme Corp (verified via Domain Linkage, registered as a node in the hierarchy)
- Acme Corp can then issue: Employee Verifiable Credentials
Any company can issue Verifiable Credentials on its own, that is how the W3C standard works. But being part of the IOTA Hierarchy adds an additional layer of trust: LinkedIn (or another intermediary) certifies that the company is a real, verified entity within the federation. It is the difference between a self-signed certificate and one issued by a trusted certificate authority. Both work, but one carries more weight because a recognized party vouches for it.
Nothing prevents multiple federations from interoperating. LinkedIn could run its own hierarchy, and so could other trusted third parties, industry associations, government registries, professional certification bodies. Because the underlying standard is the same (W3C DIDs and IOTA Hierarchies), these federations can recognize each other. This means you could verify not just whether a company is accredited by LinkedIn, but how many independent federations recognize it. The more federations vouch for an entity, the stronger the trust signal.
Step 4: Employees Receive Verifiable Credentials
The organization issues W3C Verifiable Credentials to their employees. A credential for Jane Doe would contain:
- "Jane Doe is employed as VP Engineering at Acme Corp"
- "Issued by: Acme Corp (present in LinkedIn IOTA Hierarchies)"
- "Cryptographically signed by the issuer's DID, which is bidirectionally linked with the
acme.comdomain"
The employee stores this credential in their digital wallet. They control it. They choose when and where to present it. LinkedIn itself could manage the Verifiable Credentials on behalf of users, integrating the verification flow directly into the platform experience.
Step 5: Anyone Can Verify, No One Can Fake
When Jane connects with you on LinkedIn (or any platform), her professional identity can be verified by:
- Checking her Verifiable Credential - Is it cryptographically valid?
- Tracing the issuer - Is Acme Corp an accredited node in LinkedIn's IOTA Hierarchy?
- Verifying Domain Linkage - Is Acme Corp's DID bidirectionally linked to
acme.com?
If all three checks pass, you have cryptographic proof that Jane works at Acme Corp. No AI-generated headshot, stolen profile, or social engineering can fake this chain. LinkedIn could perform this verification automatically and display a trust badge on verified profiles.
What Makes This Practical for Enterprises
This is not a theoretical exercise. Here is why this approach is ready for real-world adoption.
Low cost - The only on-chain costs are for generating DIDs and registering the company on IOTA Hierarchies. Each transaction costs approximately 0.005 IOTA, a decimal amount. Once the company is registered in the hierarchy, issuing Verifiable Credentials to employees does not require additional on-chain transactions.
No blockchain expertise needed for employees - Employees do not interact with the blockchain. They receive a credential in their wallet, the same way they would receive a digital badge today. IOTA Gas Station can sponsor transaction fees, so end users never need to hold crypto.
Standards-based and interoperable - W3C DIDs and Verifiable Credentials are open standards. Credentials issued on IOTA are not locked into IOTA. Any system that supports W3C VCs can verify them.
Enterprise key management - IOTA Secret Storage ensures private keys never touch the application layer. Organizations can integrate with their existing HSM/KMS infrastructure.
GDPR compliant - Employee personal data is never stored on-chain or exposed publicly. The Verifiable Credential is held by the employee (or managed by the LinkedIn platform on their behalf) and only shared when they choose to present it. The on-chain data is limited to the organizational hierarchy and DID references, not personal information.
Revocable - When an employee leaves the company, the organization revokes their credential on-chain. The revocation is instant and publicly verifiable.
The Bigger Picture: Filling the Trust Layer
The LinkedIn fake account problem is a symptom of a larger issue: the internet has no native trust layer for professional identity.
We trust websites because of TLS certificates. We trust financial transactions because of regulated intermediaries. But we have no equivalent mechanism for professional identity. We rely on platforms (LinkedIn, email, corporate directories) that can be spoofed, hacked, or simply wrong.
Decentralized identity fills this gap. When enterprises adopt DIDs with Domain Linkage and issue Verifiable Credentials to their employees, they create a trust layer that:
- Works across any platform (not just LinkedIn)
- Is cryptographically verifiable (not just "looks legitimate")
- Is controlled by the organization (not by a third-party platform)
- Is revocable in real-time (not dependent on platform moderation)
The IOTA Foundation is actively working to build this infrastructure. Their Web3 Identification Solution was selected for the European Blockchain Sandbox, validating the approach at the EU regulatory level.
Companies like Impierce are already building production-grade tooling for DID and Verifiable Credential management, making it easier for enterprises to integrate decentralized identity into their existing systems.
The vision is straightforward: fill the trust layer with verifiable base data. Once enterprises register their organizational hierarchies and issue credentials to employees, the data exists for any platform to leverage. LinkedIn could verify professional claims. Job boards could filter out fake applicants. Enterprise systems could authenticate partners automatically.
What Needs to Happen
For this to work at scale, three things need to happen:
-
Enterprises adopt DIDs with Domain Linkage - This is the foundation. Every organization needs a verified DID linked to their domain. The technical barrier is low, but awareness and adoption need to grow.
-
Credential issuance becomes standard HR practice - Issuing a Verifiable Credential should be as routine as issuing a corporate email address. The onboarding cost is minimal, and the security benefits are significant.
-
Platforms integrate verification - LinkedIn, job boards, and professional networks need to support Verifiable Credential verification. This does not require them to build on any specific blockchain. W3C standards ensure interoperability.
None of these steps require replacing existing systems. This is additive infrastructure. You keep your LinkedIn profile, your corporate email, your existing HR systems. You add a cryptographic proof layer on top.
Want to implement decentralized identity for your organization? Our team has hands-on experience with IOTA Identity, IOTA Hierarchies and Key Management Systems.
Request a Free ConsultationConclusion
LinkedIn's fake account problem will not be solved by better AI detection or faster account removal. It will be solved by giving organizations the tools to cryptographically verify their employees' professional identities.
The technology exists today. IOTA Identity, Hierarchies, and IOTA Gas Station provide a complete solution. The cost is negligible. The security improvement is fundamental.
The question is not whether professional identity will move to verifiable credentials. The question is which enterprises will adopt it first and gain the trust advantage.
Need help implementing IOTA Trust Framework?
Schedule a free consultation to explore how KChain Solutions can help your organization implement production-grade blockchain architecture.

Valerio Mellini
Founder & IOTA Foundation Solution Architect
10+ years in software architecture across Accenture, PwC, Wolters Kluwer, and Ubiquicom. Certified Blockchain Solutions Architect. Helping enterprises implement production-grade blockchain systems with architecture-first methodology.